Order Backlinks Online, Buy Backlinks Building Cheap And Get Quality Link Building Services From 724ws Co.
We tested it and so far there is probably no other quality SEO Backlinks Services package to buy, which have so much ranking power, Improve your website ranking and SEO with high PR WEB2.0 Backlinks and high DA backlinks cheap in it.
Buy Backlinks, Buying Dofollow Backlinks, Get high Pr Backlinks, permanent Links, Buy Backlinks Online with niche relevant fresh articles, relevant images and 300-350 words included.
Buy PBN Backlinks
$ 10
One- TimeBuy Link PyramidMost Popular
$ 120
One- Time6500 Permanent Links
2000 Relevant Posts
WEB2.0-PBN-Forum-EDU
Dofollow- Nofollow
Permanent Links
Order NowBuy EDU Backlinks
$ 125
One- Time150 EDU GOV BackLinks
300 PR9 Backlinks
1 URL + 10 Keywords
Dofollow- Nofollow
Permanent Links
Order NowBuy SEO Service
$ 1200
One- TimeAny Kind Of Websites
Easy To Hard Keywords
CTR Improvement
Dofollow- Nofollow
Permanent Links
Order NowBuy Backlinks With Bitcoin (BTC)- Get 5% Extra
 Good news to all users who asked us to accept bitcoin (btc) and Webmoney to buy PBN backlinks services, I’m glad to say that we now accept all three payment gateways and you can easily choose your payment method on your shopping cart and Buy EDU Backlinks !!!.
Good news to all users who asked us to accept bitcoin (btc) and Webmoney to buy PBN backlinks services, I’m glad to say that we now accept all three payment gateways and you can easily choose your payment method on your shopping cart and Buy EDU Backlinks !!!.
Many countries do not use PayPal because of their banking or governmental policies, and now customers from these countries can easily buy our services and get 5% extra credit.
Fund Your wallet upto 300$ and get 400$ credit.
Increase website traffic with quality link building
How Quality Link Building Can Help Increase Website Traffic
Link building is an essential part of any successful SEO strategy.
Quality backlinks building can help increase website traffic by improving your website’s visibility in search engine results pages (SERPs).
Quality backlinks are those that come from authoritative websites and are relevant to your website’s content.
Quality PBN backlinks can help boost your website’s ranking in SERPs, which can lead to more website visitors.
-
Sale!
Buy Backlinks For Gambling And Casino
Original price was: $450.$380Current price is: $380. -
Buy Backlinks In 2 Layer Link Pyramids For SEO
$85 – $250 -
Buy Blog Comments backlinks- Verified Comment backlinks
$25 – $70 -
Sale!
Buy EDU GOV Backlinks For SEO
Original price was: $135.$125Current price is: $125. -
Buy Forum Backlinks Dofollow
$40 – $110 -
Buy High Da Dr Pr Backlinks With Relevant Articles
$130 – $900 -
Buy High Quality Super Strong Backlinks DA-PA=81-64 Alexa=790
$450 – $850 -
Buy Link Pyramid Backlinks For SEO
$120 – $195 -
Buy Nofollow PBN DA-PA 20-70 Permanent Backlinks On TF 20+ Manually
$10 – $80 -
Buy PBN Backlinks Permanent PBN
$10 – $120 -
Buy SEO backlinks High da Diverse Links
$200 – $300 -
Sale!
Buy Social Network Backlinks
Original price was: $250.$199Current price is: $199.
Buy Link Pyramid Backlinks To Rank Google 1th Page
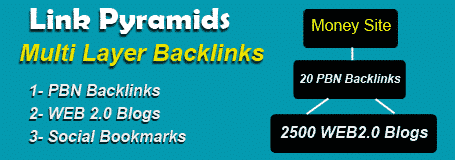 We Provide 2 and 3 Tier Buy Link Pyramid Backlinks.
We Provide 2 and 3 Tier Buy Link Pyramid Backlinks.
Special Theme Designed By 724ws SEO Team Is Tested On Many Projects.
The Significant Difference From Other Themes Is Buy PBN Backlinks On First Layer (buy backlinks seo).
We Use DA 40-75 Qualified Dofollow PBN Backlinks As Layer 1 On All Link Pyramids Themes.
we use premium fast indexer for all links and urls to make it rank your site faster.
Buy PBN backlinks For Your Website
 Niche relevant articles contain over 300 words and are 100% unique, makes your backlink index faster. we also put a relevant image for every article to make it natural and safe.
Niche relevant articles contain over 300 words and are 100% unique, makes your backlink index faster. we also put a relevant image for every article to make it natural and safe.
Aged domains hosted on various ips and countries is a significant factor for our pnb different.
All PBN Backlinks websites are designed with different responsive themes and have real visitors. (buy backlinks cheap) we do all your site SEO needs to dominate search engines and increase your ranking cheap.
Link Building Strategies For Site SEO
 Creating Quality Content for Link Building:
Creating Quality Content for Link Building:
Quality content is essential for link building.
By creating content that is informative, engaging, and relevant to your target audience, you can attract links from other websites and social media users.
Additionally, you can use content to build relationships with other industry experts and influencers.
Guest Posting for Link Building:
Guest posting is a great way to build links to your website.
By writing content for other websites, you can gain backlinks from those websites and increase your website’s visibility.
Additionally, you can use guest posting to build relationships with other industry experts and influencers.
Buy Quality Backlinks naturally
 How to Use Natural Link Building to Boost Your SEO
How to Use Natural Link Building to Boost Your SEO
Natural link building is an important part of any SEO strategy.
It involves creating links from other websites to your own, which can help to increase your website’s visibility and rankings in search engine results.
Natural link building is a great way to get more traffic to your website, as well as to build relationships with other websites and businesses.
Here are some tips on how to use natural link building to boost your SEO.
Make your Backlinks in wide time intervals and avoid to put huge backlinks in a day or a short timeline.
Try to buy little backlinks but continue to buy. in this way your link building will be more natural and you will certainly rank on SERP.
Buy Quality Backlinks for SEO
To figure out how to get backlinks is one of the most seasoned and best Web optimization strategies.
It’s likewise a standout amongst the most profitable approaches to developing natural inquiry traffic. In any case, you must be mindful of how to assemble high quality backlinks.
Buy Quality Backlinks have been a noteworthy piece of how Google and other search engines decide how a site is eligible to show in search results among hundreds of others.
The number of quality Backlinks and the rate of submitting, type and specification of Backlink website have made the work of link building a professional job..
Why Choose Us As Your SEO Expert?
- Because We are always online to support you.
- Our Backlinks services prices are very low
- We provide really permanent backlinks
- Your Orders delivers on time
- Each Order has extra links (bonus)
- We guaranty what we claim
- Our SEO Experience is over 15 years
- Also we are always updated with SERP Algorithms
- And so much much more…
Get Free Credits By Ordering First Time
- Get $1 Credit At Your First Purchase Backlinks.
- Get $1 Every Day You Visit Our site (Active Buyers With over 100$ Order/month).
- Get $1 When You Write Product Review.
- We Will Put More Free Credit Options Soon.
- Please do not use fake proxies to get visits.
Get 5% More Money If You Topup Your Wallete
- Easy to order multiple backlinks services.
- Paypal + Webmoney + Bitcoin Payment Gateways.
- Fast and secure.
- Ability to send money to other users.
Buy Backlinks Cheap Using Quality Social Bookmarking Site
Buy backlinks cheap Social media is an important part of any successful SEO strategy.
By leveraging the power of social networks backlinks, you can create backlinks to your website that will help boost your SEO rankings.
Backlinks are links from other websites that point to your website, and they are an important factor in determining your website’s ranking in search engine results.
By creating backlinks cheap from social networks, you can increase your website’s visibility and reach a wider audience.
Here are some tips on how to use social network backlinks to boost your SEO.
What Are Social Network cheap Backlinks And How Do They Work?
Social network backlinks are links from other social networking platforms to your website.
Quality backlinks are important for website promotion and increasing website traffic.
They are also important for providing search engine optimization (SEO).
Social network backlinks can be obtained from popular social networking sites such as Twitter, Facebook, LinkedIn, etc.
When users on these sites share links, posts, and other pieces of content from your website, this sends out a signal about the quality of your website and its content.
When another site links to your website, this tells search engine algorithms that your content is of high quality, thus boosting your website’s ranking in search engine results pages.
This then allows more people to find and visit your website, which helps to increase traffic. Backlinks also help build relationships between your website and those of other influential sites and can even lead to improved brand recognition.
The most popular social networks are Facebook, Twitter, Instagram, and YouTube.
These networks have millions of users, and they are a great way to create backlinks to your website.
You can post content on these networks that link back to your website, or you can create ads that link to your website. You can also use these networks to engage with your audience and build relationships with potential customers.
A good quality seo backlinks can be purchased very easily.
A good thing to do is to add a news section to your website, where you publish your companies Press Releases filed under the “in the news” category.
The British Business and General Aviation Association is an association that is concerned with representing the interests of overseas affiliates and member companies to support and promote the aviation industry in the UK.
Much of business involves inducing people to buy backlinks cheap do what we want them to do.
Hashtags are a great way to increase the visibility of your content on social networks.
When you use hashtags, your content is more likely to be seen by a wider audience. You can use relevant hashtags to your industry or topic to increase the chances of your content being seen.
You can also use popular hashtags to increase the visibility of your content. By using hashtags, you can create backlinks to your website and increase your SEO rankings.
Search engines have become quite adept at sniffing out spammy backlinks so do not buy backlinks cheap from spammy sites., and they will penalize any site that makes use of them.
Search Engine Optimization And Your Online Presence with seo backlinks focus
Search engine optimization (SEO) is a powerful tool for improving your online presence.
SEO is the process of optimizing your website and content to make it more visible to search engines, which in turn can help you reach more potential customers.
SEO involves optimizing your website’s content, structure, and code to make it easier for search engines to find and index your website.
Additionally, SEO can help you create content that is more relevant to your target audience, which can help you build trust and credibility with your customers.
By optimizing your website for search engines, you can increase your visibility and reach more potential customers.
Tips for Optimizing Your Online Presence with SEO
If you want to optimize your online presence with SEO, there are a few tips you should keep in mind.
- First, make sure your website is optimized for mobile devices. Mobile optimization is essential for SEO because more and more people are using their phones to search for information.
- Additionally, make sure your website is easy to navigate and has a clear structure. This will make it easier for search engines to crawl and index your website.
- Finally, create content that is relevant to your target audience. This will help you build trust and credibility with your customers.
So if you’ve gotten this far, you should know a lot of information about how search engines rank websites and about how you can position your own site and business to generate more search traffic from search engines like Google.
Buy BackLinks SEO Pro will take whatever keywords you feed in, then find sites, buy forum backlinks, blogs, socials etc that will allow posting of link backs (there’s millions of them).
Always remember that the best way to maximize the function of link is not to focus on the quantity, but the quality.
The Benefits of Optimizing Your Online Presence with SEO
Optimizing your online presence with SEO can have many benefits.
First, it can help you reach more potential customers. SEO can help you increase your visibility in search engine results, which can help you reach more people.
Additionally, SEO can help you create content that is more relevant to your target audience, which can help you build trust and credibility with your customers. Finally, SEO can help you improve your website’s performance, which can help you increase your conversions and sales.
By optimizing your website for search engines, you can improve your online presence and reach more potential customers.
Create a solid long tail SEO plan for your products. Understanding the target audience is a primary consideration for SEO in general and for keywords in particular.
Usage of right keywords is the main source of generating traffic and buy backlinks cheap for them.
Google has built up its calculations so it is currently utilizing mental weight – when you get new Buy backlinks SEO, initial your rankings drop down, and just with some time they return and get higher than some time recently.
What Is Link Pyramid Backlinks
Link Pyramid backlinks are one of the first link building strategies to be created as far as Google started setting backlinks as an incentive on search results ranking.
The backlink pyramid is very simple to clarify and helpful from multiple points of view.
The procedure enables you to send superb backlinks to your Money sites , fortifies those amazing connections, and enhances the listed rate of those backlinks.
In this article, we will clarify what precisely Link Pyramid Backlinks is and how to make it.
Structure of a link Pyramid:
 The structure is quite simple. It is a layered structure which resembles a pyramid with the most backlinks in the base level (tier 3) and a minimal amount of backlinks at the top level.
The structure is quite simple. It is a layered structure which resembles a pyramid with the most backlinks in the base level (tier 3) and a minimal amount of backlinks at the top level.
Here, you can see a graph of a link pyramid.
Most SEO experts use backlink pyramid with three levels:
Level 1:
Level 1 will be your most elevated quality Links. These Links should be Manually made Web 2.0‘s backlinks, high PR blog entries, high PR social bookmarks, and so on…
These Backlinks will point specifically my website so you need to ensure they are not spam (buy backlinks seo).
Level 2 Backlinks:
The second-level of Links will be mid-range quality links.
You can utilize well-spun substance and auto make Backlinks. Article Directories, wiki websites, and different low PR backlinks are useful for the second-level.
Your second-level of links will point your first level of buy backlinks as it were. (buy backlinks).
The objective of the second-level is to reinforce the nature of your level 1 points and enhance the page rank (PR) or page authority (PA) of them.
Level 3 backlinks:
Level 3 needs low-quality edu Backlinks like auto-generated blog comments, social bookmarks, and Wiki links.
This third level of backlinks will point straightforwardly to your second-level of backlinks.
The objective of level 3 backlinks is to enhance the authority of your level 2 backlinks.
Most of your level 3 backlinks won’t be indexed by Google so you ought to make enough that you will have somewhere around a couple backlinks recorded per level 2 backlinks by and large.
Send another 10 to multiple times more backlinks indicating your level 2 Links (buy backlinks cheap) as you made already.
Rank Your Site Using Quality PBN Backlinks
PBN Backlinks Stands For Private Blog Network and is a system of High Authority sites used to Create Backlinks to your website (Money Site) to rank higher in the Google and other Search Engines as well.
The Most Important Point Of view about PBN Backlinks is that every one of the individual PBN Sites is not linked to another one at all.
They are not related to each other, therefore you will have natural backlinks from different websites with various content and location.
Do PBN Backlinks Still Work?
There is a statement from Matt Cutts when gotten some information about backlink significance from the calculation.
What makes this technique viable is the sites that shape a PBN are viewed by Google as legitimate.
You are not accepting backlinks from some new site, nor a spammy one, you are getting links from Authority and famous site and Google’s Algorithm adores it.
That is basically, how we find PBN Domains.
Between 15,000 – 20,000 Domain expires each day, a significant number of which will have great ‘measurements’ for a PBN.
There are 4 primary measurements to use for estimating PBN.
These are…
DA Stands For Domain Authority by Moz.com
PA Equals Page Authority by Moz.com
TF – Trust Flow by Majestic.com
CF – Citation Flow by Majestic.com
I don’t know how exactly they work but I know these factors are very important for choosing to Buy PBN Backlinks to trust and buy backlinks seo.
- DA estimates Domain Authority, depends on the backlinks to it.
- PA measure how trustworthy and authority of a page on the site is, It depends on the Number of backlinks to it. PA Also is affected by the DA of the site.
- TF measures the Authority and Trustworthy of the sites Links.
- CF estimates how powerful the links to the site are.
Here is a fast reference control on what to search for:
DA – 19+
TF – 11+
CF – 15+
I have also tested Domains weaker than this on various projects and results was fine, however, this is the general rule I attempt to tell you.
But you can have your own measurement don’t worry about following me.
Referring Domains – A metric that demonstrates the quantity of sites that links to your domain.
over 30 is sufficient here.
Backlinks – This is the quantity of Links the site has. It is different from referring domains.
if you link 3 times from a site you have 3 edu gov backlinks and 1 referring domain backlinks.
Anchor Text– This is the content individuals use when Linking to the site. (buy backlinks cheap for your website)
Many Ways To Build Backlinks To Your Website For Free
Build backlinks Like, guest posting (blog Posts) has always worked and will continue to work as long as the backlink you add provides value to the website.
Yes, you are actually going to have to do more work! You can even work with an security alarm for alerts.
Even better if it contains the keyword you are targeting, as this will help boost your rankings by buy backlinks cheap.
You can even find one that’s BPA-free. You need to take your way on these authorizations so to find your operation, not just an exact one, but legal as well.
A standout brand is the best way to attract their attention, but first, you need to know exactly who your customers are and what appeals to them. (buy backlinks seo)
You can use VoIP to fully integrate your desktop and your mobile phone service, reducing the need for additional mobile phones.
Can you really get an authentic, accurate, insightful and TRUTHFUL psychic reading on the telephone. without leaving your home?
Buy backlinks cheap to your site is a great way to raise your page rank and get more visibility in search results.
While this isn’t exactly a free means of building high da link pyramid backlinks, the cost is very minimal, and the results should pay for themselves rather quickly buy backlinks cheap.
The stability of enterprise and your household isn’t something people actually so and consider casually.
This is a cheaper way of expanding your business, hassle free and no need to build a new office.
Note: Making sure you have the adequate space for your mail room needs is the first step in getting the equipment you need.
Go and signal up for things you already have accessibility to. In today’s economy, most economic boundaries have already disappeared and those remaining will continue to diminish.
To make this more effective, you should also link your content after it is published by the network. (buy backlinks cheap)
I think it is fair to say that the number one problem the majority of Internet marketers face is how to get more website traffic.
Getting your content distributed is one powerful way to get both edu backlinks and traffic to your blog.
Time Management is one of the most critical aspects of running a home business.
The strategic plan of an organization or a nation is incomplete unless it includes the integration of crisis management.
There is hyperlink code that is called out either as “nofollow” or “dofollow,” and that will either allow or not allow PR to pass (buy backlinks cheap).
This will also enable your waiters to place orders as well as pick up completed plates.
Our SEO Link Building Services
Link Pyramid 2 Layer Backlinks Contains Various Type of links
This link pyramid package contains 2 parts. First layer contains PBN- WEB2.0- EDU- GOV Backlinks– Dofollow Article Submission, And Second Part contains over 4000 premium social bookmarks, PDF directory, blog comments, dofollow articles.
On-Page and Off-Page SEO Professional Service
SEO has 2 major part, first and the most important part is on-page SEO. This part contains all corrective actions on your website pages to make them visible by search engines.
Second part or off-page SEO contains all external link building in other sites and social networks to increase your website authority and force search engines to rank your website according to your site content and keywords.
Private Blog Networks (PBN) Backlinks
PBN backlinks package is provides with many options in number of PBN Backlinks websites from 10 to 200 high authority (PA-DA-DR) websites.
For each keyword we write a relevant post and put your link in it. Backlinks are one of the most crucial elements of successful search engine optimization (SEO) strategies.
PBN Backlinks are one type of backlink that can take a website’s SEO rankings to the next level. However, they must be used correctly to truly benefit your website’s SEO efforts.
WEB2.0 High Authority Backlinks Package
This service provide 100 to 1000 high quality web 2.0 backlinks. Web2.0 websites have huge daily traffic and high da.
Web2.0 backlinks are especially powerful because they come from websites that are highly trusted by search engines.
These websites are usually popular and have a lot of content, which makes them more likely to be indexed by search engines.